The field of hardware security has witnessed a paradigm shift with the emergence of Physical Unclonable Functions (PUFs), creating what many experts call a "silicon fingerprint" revolution. These unique hardware-based security primitives leverage the inherent randomness in manufacturing variations to generate device-specific responses that cannot be physically cloned or mathematically predicted. As we move deeper into the era of IoT and edge computing, researchers are developing novel PUF structures that push the boundaries of what was previously thought possible in hardware authentication and cryptographic key generation.
The fundamental premise of PUF technology lies in its ability to transform microscopic manufacturing variations - traditionally considered undesirable - into a powerful security feature. Unlike traditional cryptographic approaches that rely on stored digital keys, PUFs derive their security from the physical characteristics of the hardware itself. This intrinsic security mechanism has sparked a wave of innovation in PUF architectures, with researchers exploring increasingly sophisticated structures that offer improved reliability, uniqueness, and resistance to modeling attacks.
Recent advancements in PUF structures have moved beyond conventional delay-based and memory-based designs. One particularly promising direction involves hybrid PUF architectures that combine multiple physical entropy sources to create more robust security primitives. These next-generation PUFs might integrate optical characteristics with electronic properties, or combine memristor technologies with traditional CMOS structures, creating multi-factor authentication mechanisms that exist nowhere else in nature.
The development of reconfigurable PUF structures represents another significant leap forward. Unlike static PUFs that produce fixed responses, these dynamic architectures can be intentionally modified to generate new challenge-response pairs while maintaining their fundamental unclonability. This capability addresses one of the long-standing limitations of early PUF implementations - the finite set of usable challenges - while introducing new possibilities for forward-secure cryptographic applications.
At the nanoscale level, researchers are exploring quantum-inspired PUF structures that exploit quantum mechanical phenomena in semiconductor devices. These approaches go beyond merely using quantum effects as entropy sources; they aim to create authentication protocols where the security can be mathematically proven based on physical principles. While still in experimental stages, such quantum PUFs could potentially offer security guarantees that are fundamentally impossible to achieve with classical cryptographic systems.
Another exciting development comes in the form of self-healing PUF structures designed to maintain stability despite environmental variations and aging effects. Traditional PUFs often struggled with reliability issues caused by temperature fluctuations or device degradation over time. The new generation of self-correcting architectures incorporates on-chip compensation mechanisms and adaptive algorithms that preserve the PUF's unique signature while filtering out noise and drift.
The integration of machine learning techniques with PUF design has led to cognitive PUF structures that can actively resist modeling attacks. Rather than simply relying on the complexity of the physical system, these intelligent PUFs can detect patterns in attack attempts and dynamically adjust their response behavior. This creates a moving target for would-be attackers, significantly raising the bar for successful physical or mathematical cloning attempts.
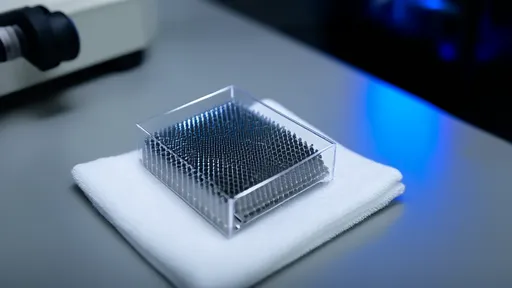
In the realm of practical applications, we're seeing novel three-dimensional PUF structures that exploit variations in stacked die configurations or through-silicon vias (TSVs). These 3D architectures provide orders of magnitude more challenge-response possibilities compared to planar designs, while also benefiting from the inherent randomness in vertical interconnects. For high-security applications, such 3D PUFs offer an attractive combination of physical complexity and compact form factor.
Emerging research into photonic PUF structures suggests another promising avenue for future development. By leveraging the unique scattering patterns created when light interacts with deliberately engineered optical structures, these PUFs could provide ultra-fast authentication with extremely low power consumption. Such photonic implementations might prove particularly valuable for securing next-generation optical communication networks and quantum computing interfaces.
The development of biologically-inspired PUF structures represents one of the more unconventional approaches gaining traction. Drawing inspiration from biological systems that exhibit natural uniqueness (such as fingerprints or retinal patterns), these PUFs mimic the complex, multi-layered randomness found in nature. Some experimental designs even incorporate organic materials or biomolecular components to achieve physical characteristics that are inherently difficult to reproduce artificially.
As PUF technology matures, we're witnessing the emergence of application-specific PUF structures tailored for particular use cases. Automotive systems might employ PUFs designed to withstand extreme temperature ranges, while medical implants could utilize biocompatible PUF structures that remain stable in vivo. This specialization trend reflects the growing sophistication of PUF technology as it moves from laboratory curiosity to mainstream security solution.
The security implications of these new PUF structures extend far beyond simple device authentication. Advanced architectures now enable hierarchical security schemes where different PUF responses can be used for different security functions within the same device. One response might serve as a root encryption key, while another could control access to secure boot functions, and yet another might manage hardware feature enablement - all derived from the same physical structure but mathematically isolated from one another.
Looking ahead, the convergence of PUF technology with other cutting-edge semiconductor developments promises even more revolutionary structures. The integration of PUFs with neuromorphic computing elements could lead to hardware that not only authenticates itself but also adapts its security posture based on usage patterns and threat detection. Similarly, the combination of PUF structures with emerging non-volatile memory technologies might enable entirely new paradigms in secure, unclonable storage.
While the theoretical foundations of PUF technology are well-established, the practical implementation of these new structures presents significant engineering challenges. Issues such as environmental stability, response uniformity, and manufacturing yield require careful consideration in any new PUF design. The most successful next-generation PUFs will likely be those that find the optimal balance between physical complexity and practical manufacturability.
The standardization efforts surrounding PUF technology are also evolving to accommodate these new structures. As the diversity of PUF implementations grows, the security community faces the challenge of developing evaluation methodologies that can properly assess the robustness of fundamentally different architectures. This standardization push is critical for building trust in PUF-based security solutions across industries.
In conclusion, the landscape of PUF structures is undergoing a period of rapid innovation, driven by both advancing semiconductor technologies and growing security requirements. From quantum-inspired designs to biologically-mimetic architectures, these new PUF implementations are expanding the boundaries of hardware-based security. As research progresses, we can expect to see PUF technology transition from being primarily an authentication tool to becoming a fundamental building block for next-generation secure computing architectures across all segments of the digital economy.

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025
By /Jul 29, 2025
By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025
By /Jul 29, 2025

By /Jul 29, 2025

By /Jul 29, 2025
By /Jul 29, 2025
By /Jul 29, 2025